Updates
- [2023.3.1] The name of this EIP might be changed according to the suggestions
- [2023.3.9] Submit some updates and add the source codes for trying.
- [2023.3.20] The updates have been merged. The latest version can be found here
- [2023.4.6] Slim down and make the presentation more succinct. We are preparing the first Demo of an
ERC-6358token. - [2023.4.18] Add a detailed analysis for the
double-spend attackissue. - [2023.5.30] Update the implementation examples
- [2023.6.1] A simple Testnet (Demo) to try the first ERC-6358 tokens. The related front can be found at the Omniverse Demo, and we are preparing the related auto-deployment tools.
- [2024.2.28] It’s a long time to update, as in the last 8 month, we are building a zk-based omni-executor mentioned here for this protocol. The zk-related components are based on plonky2 and now we have finished a basic version of it. Next, we will make some optimization of the performance and this will be opensoure soon.
- [2024.5.16] A testnet based on erc-6358 has been launched. plonky2 is used to generate recursive proofs in
FRI, and Halo2 based stark verifier is used to generate the finalKZGproof, which is more friendly to on-chain smart contracts. Part of the code of the circuit is open sourceed
Abstract
The ERC-6358 (Omniverse DLT) is a new application-level (ERC) token protocol built upon multiple existing L1 public chains, enabling asset-related operations such as transfers and receptions running globally and synchronously over different consensus spaces.
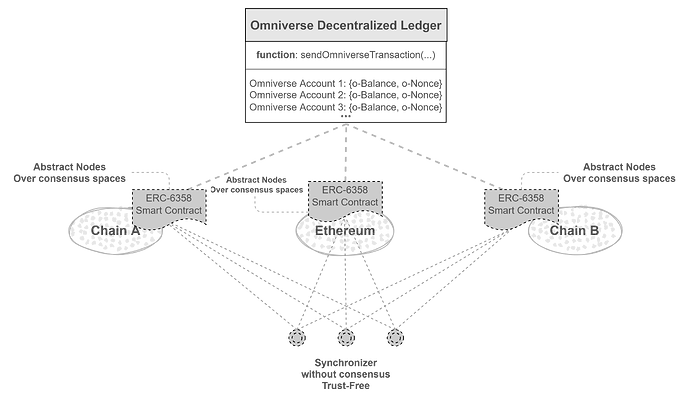
Figure.1 Architecture
Motivation
- The current paradigm of token bridges makes assets fragment.
- If tokens like ETH were transferred to another chain through the current token bridge, if the chain broke down, it will be lost for users.
The core of ERC-6358 is synchronization instead of bridge-transferring, even if all the other chains break down, as long as one chain is still running, user’s assets will not be lost.
- The fragment problem will be solved.
- The security of users’ multi-chain assets can be greatly enhanced.
Rationale
With ERC-6358, we can create a global token protocol, that leverages smart contracts or similar mechanisms on existing blockchains to record the token states synchronously. The synchronization could be made by trustless off-chain synchronizers.
Architecture
As shown in Figure.1, smart contracts deployed on different chains execute o-transactions of ERC-6358 tokens synchronously through the trustless off-chain synchronizers.
- The
ERC-6358smart contracts could be referred to as Abstract Nodes. The states recorded by the Abstract Nodes that are deployed on different blockchains respectively could be considered as copies of the global state, and they are ultimately consistent. - Synchronizer is an off-chain execution program responsible for carrying
o-transactionsfrom theERC-6358smart contracts on one blockchain to the others. The synchronizers work trustless as they just delivero-transactionswith others’ signatures, and details could be found in the workflow.
Principle
-
There should be a global user identifier for
ERC-6358, which is recommended to be referred to as Omniverse Account (o-accountfor short) in this article. Theo-accountis recommended to be expressed as a public key created by the elliptic curvesecp256k1. A mapping mechanism is recommended for different environments. -
The synchronization of the
o-transactionsguarantees the ultimate consistency of token states across all chains. The related data structure can be found here:solidityand here:rust.- A
noncemechanism is brought in to make the states consistent globally. - The
nonceappears in two places, the one isnonce in o-transactiondata structure, and the other isaccount noncemaintained by on-chainO-DLTsmart contracts. - When synchronizing, the
nonce in o-transactiondata will be checked by comparing it to theaccount nonce.
- A
Workflow
- Suppose a common user
Aand her related operationaccount nonceis $k$. Ainitiates ano-transactionon Ethereum by callingIERC6358::sendOmniverseTransaction. The currentaccount nonceofAin theERC-6358smart contracts deployed on Ethereum is $k$ so the valid value ofnonce in o-transactionneeds to be $k+1$.- The
ERC-6358smart contracts on Ethereum verify the signature of theo-transactiondata. If the verification succeeds, theo-transactiondata will be published by the smart contracts on the Ethereum side. The verification includes:- whether the balance (FT) or the ownership (NFT) is valid
- and whether the
nonce in o-transactionis $k+1$
- The
o-transactionSHOULD NOT be executed on Ethereum immediately, but wait for a time. - Now,
A’s latest submittednonce in o-transactionon Ethereum is $k+1$, but still $k$ on other chains. - The off-chain synchronizers will find a newly published
o-transactionon Ethereum but not on other chains. - Next synchronizers will rush to deliver this message because of a rewarding mechanism. (The strategy of the reward could be determined by the deployers of
ERC-6358tokens. For example, the reward could come from the service fee or a mining mechanism.) - Finally, the
ERC-6358smart contracts deployed on other chains will all receive theo-transactiondata, verify the signature and execute it when the waiting time is up. - After execution, the
account nonceon all chains will add 1. Now all theaccount nonceof accountAwill be $k+1$, and the state of the balances of the related account will be the same too.
Reference Implementation
Omniverse Account
- An Omniverse Account example:
3092860212ceb90a13e4a288e444b685ae86c63232bcb50a064cb3d25aa2c88a24cd710ea2d553a20b4f2f18d2706b8cc5a9d4ae4a50d475980c2ba83414a796- The Omniverse Account is a public key of the elliptic curve
secp256k1 - The related private key of the example is:
cdfa0e50d672eb73bc5de00cc0799c70f15c5be6b6fca4a1c82c35c7471125b6
- The Omniverse Account is a public key of the elliptic curve
Mapping Mechanism for Different Environments
In the simplest implementation, we can just build two mappings to get it. One is like pk based on sece256k1 => account address in the special environment, and the other is the reverse mapping.
The Account System on Flow is a typical example.
Flowhas a built-in mechanism foraccount address => pk. The public key can be bound to an account (a special built-in data structure) and the public key can be got from theaccount addressdirectly.- A mapping from
pkto theaccount addresson Flow can be built by creating a mapping{String: Address}, in whichStringdenotes the data type to express the public key and theAddressis the data type of theaccount addresson Flow.
Security Considerations
Attack Vector Analysis
According to the above, there are two roles:
- common users who initiate a
o-transaction(at the application level) - and synchronizers who just carry the
o-transactiondata if they find differences between different chains.
The two roles might be where the attack happens:
Will the synchronizers cheat?
-
Simply speaking, it’s none of the synchronizer’s business as they cannot create other users’ signatures unless some common users tell him, but at this point, we think it’s a problem with the role common user.
-
The synchronizer has no will and cannot do evil because the transaction data that they deliver is verified by the related signature of others(a common user).
-
The synchronizers will be rewarded as long as they submit valid o-transaction data, and valid only means that the signature and the amount are both valid. This will be detailed and explained later when analyzing the role of common user.
-
The synchronizers will do the delivery once they find differences between different chains:
- If the current
account nonceon one chain is smaller than a publishednonce in o-transactionon another chain - If the transaction data related to a specific
nonce in o-transactionon one chain is different from another published o-transaction data with the samenonce in o-transactionon another chain
- If the current
-
Conclusion: The synchronizers won’t cheat because there are no benefits and no way for them to do so.
Will the common user cheat?
-
Simply speaking, maybe they will, but fortunately, they can’t succeed.
-
Suppose the current
account nonceof a common userAis $k$ on all chains. -
Common user
Ainitiates an o-transaction onERC-6358smart contracts onChain Pfirst, in whichAtransfers10o-tokens to an o-account of a common userB. Thenonce in o-transactionneeds to be $k+1$. After signature and data verification, the o-transaction data(ot-P-abfor short) will be published onERC-6358onChain P. -
At the same time,
Ainitiates an o-transaction with the same nonce $k+1$ but different data(transfer10o-tokens to another o-accountC) on Ethereum. This o-transaction(namedot-E-ac) will pass the verification onERC-6358smart contracts on Ethereum first, and be published. -
At this point, it seems
Afinished a double spend attack and theERC-6358states onChain Pand Ethereum are different. -
Response strategy:
- As we mentioned above, the synchronizers will deliver
ot-P-abto theERC-6358smart contracts on Ethereum and deliverot-E-acto theERC-6358smart contracts onChain Pbecause they are different although with the same nonce. The synchronizer who successfully submits the o-transaction first(or in the first few) will be rewarded as the signature is valid. - Both the
ERC-6358smart contracts onChain Pand Ethereum will find thatAdid cheating after they receivedot-E-acandot-P-abrespectively as the signature ofAis non-deniable. - We mentioned above that the execution of an
o-transactionwill not be done immediately and instead there needs to be a fixed waiting time. So thedouble spend attackcaused byAwon’t succeed. - There will be many synchronizers waiting for delivering o-transactions to get rewards. So although it’s almost impossible that a common user can submit two
o-transactionsto two chains, none of the synchronizers deliver theo-transactionssuccessfully because of a network problem or something else, we still provide a solution:- The synchronizers will connect to several native nodes of every public chain to avoid the malicious native nodes.
- If it indeed happened that all synchronizers’ network break, the
o-transactionwill be synchronized when the network recovered. If the waiting time is up and the cheatingo-transactionhas been executed, we can still revert it from where the cheating happens according to thenonce in o-transactionandaccount nonce.
- As we mentioned above, the synchronizers will deliver
-
Awill be punished (lock his account or something else, and this is about the certain tokenomics determined by developers according to their own situation). -
Conclusion: The common user maybe cheat but won’t succeed.
Copyright
Copyright and related rights waived via CC0.
Additional Information
We are a team focusing on multi-chain interoperability for years, and we have some experience and open-source contributions in this field. We are always dedicated to improving the convenience and security of the cross-chain experience, and we have proposed the first multi-chain interoperability solution Granted by W3F, with milestones all achieved.
In addition, we will provide a mechanism to make Omniverse Token compatible with current ERC20/ERC721 and native tokens, that is, omniverse tokens could be exchanged on current DEX like Uniswap with others. This is related to an abstract account smart contract mechanism, as it is highly recommended that a single EIP contain a single key proposal or new idea, we won’t describe more details about this point here but still we will provide an implementation of it.